- Partner Overview
- Partner Program
- Technology Partners
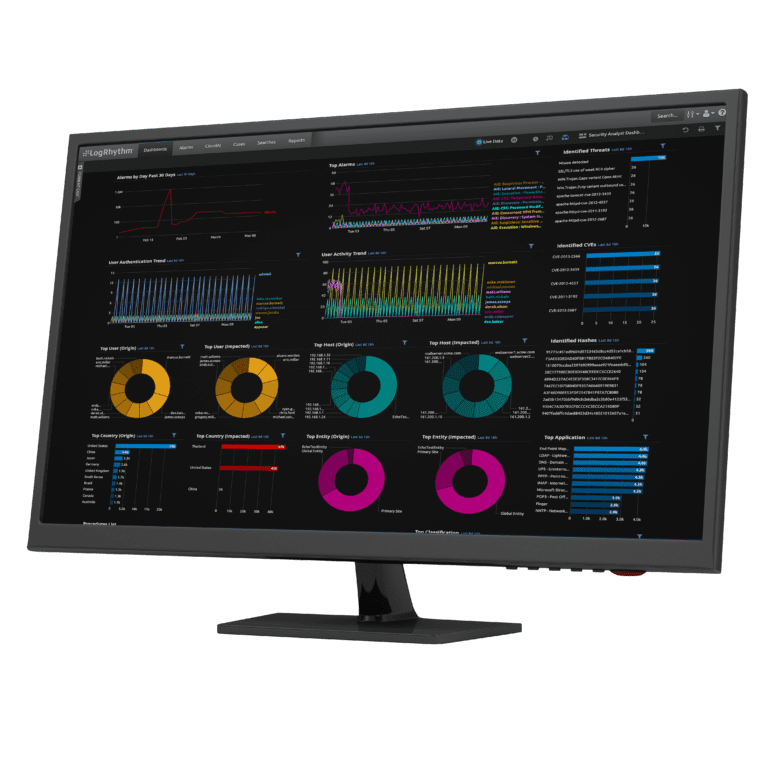
At LogRhythm, we work closely with our Technology Partners, allowing you to expand solution services including LogRhythm and leverage opportunities for better customer solutions and business growth. More options and better integration mean increased sales and happier customers.
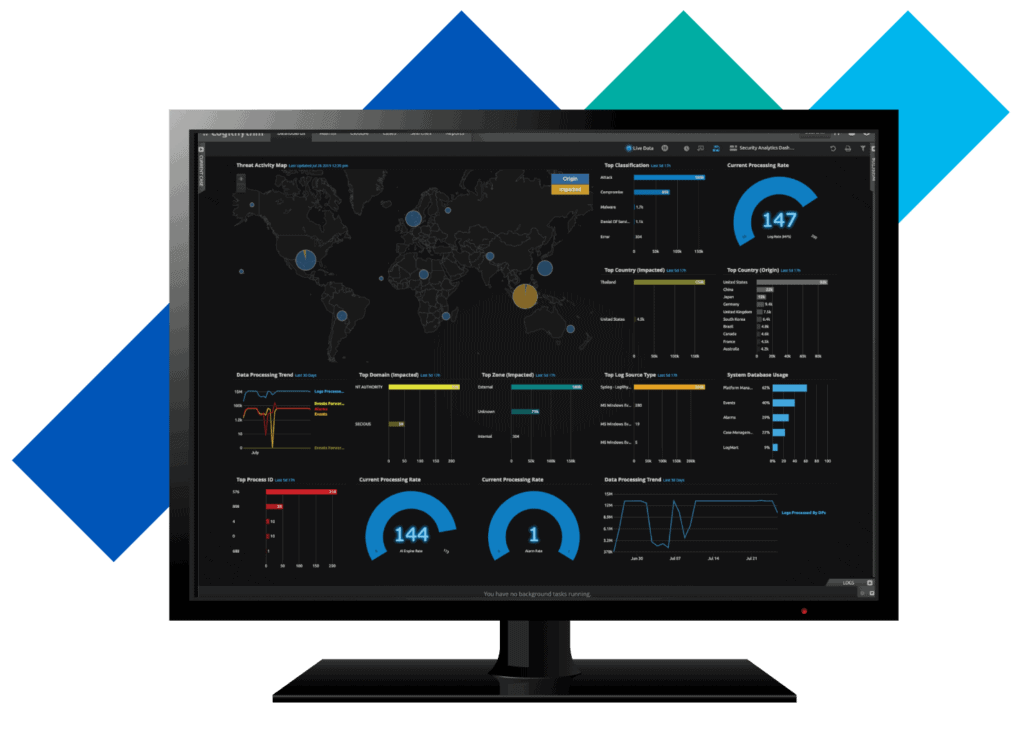
A Solution for Every Environment
Endpoint monitoring and threat detection
Cloud security monitoring
Cyber crime and fraud detection
Technology Alliance Partner Directory
A10 Networks
Amazon Web Services (AWS)

Amazon Web Services is a subsidiary of Amazon.com which offers a suite of cloud computing services that make up an on-demand computing platform. These services operate from 12 geographical regions across the world.
Anomali

AttackIQ

Balbix
Beyond Trust
BlackBerry Cylance
Cylance is revolutionizing cybersecurity with products and services that proactively prevent, rather than reactively detect the execution of advanced persistent threats and malware. Our technology is deployed on over four million endpoints and protects hundreds of enterprise clients worldwide including Fortune 100 organizations and government institutions.
Box
Broadcom
Carbon Black

Check Point Software Technologies Ltd.
Cimcor

Cisco
Code42

Cofense

Cribl
Criminal IP

Criminal IP is a threat intelligence search engine that scans the whole internet and uncovers all kinds of information on any internet connected device.
Powered by AI and Machine Learning, Criminal IP detects and assesses the risks and vulnerabilities associated with any internet connected devices in real-time. leveraging various powerful Lookup features and filters, it grants you a comprehensive view of the ever-evolving cyber risks.
CyberArk

Cyware
D3 Security
Dell
Dragos

FireEye
Forescout
Fortinet
Fortinet is a worldwide provider of network security appliances and the market leader in unified threat management (UTM). Fortinet’s products and subscription services provide broad, integrated and high-performance protection against dynamic security threats while simplifying the IT security infrastructure.
Gigamon

Google Cloud
GoTo
Infoblox
IronNet
Jamf

Jamf’s purpose is to simplify work by helping organizations manage and secure an Apple experience that end-users love and organizations trust. Jamf is the only company in the world that provides a complete management and security solution for an Apple-first environment that is enterprise secure, consumer simple and protects personal privacy. Jamf ensures secure, consumer-simple technology for over 75,300+ businesses, schools and hospitals with +32.3 million devices running Jamf.
Kaspersky
Established in 1997, Kaspersky protects over 400 million users and 240,000 companies worldwide. We transform our leading security intelligence into real protection for our clients and partners. Kaspersky empowers you to safely and confidently use technology in your life and in your business. We are a private global company, domiciled in the UK.
LOGBinder

Microsoft

Mimecast

Netskope
Okta
Outpost24
Palo Alto Networks
Picus Security
Precisely
Proofpoint
Pure Storage
Qualys, Inc.
Recorded Future
Red Seal

RevBits
SecLytics

SecureAuth
SecureAuth is a leading next-gen access management and authentication company that enables the most secure and passwordless, continuous authentication experience for everyone, everywhere. SecureAuth leverages adaptive risk analytics, using hundreds of human variables to create each user’s unique digital DNA. This enables real-time continuous authentication and provides the highest level of security throughout the digital journey.
SecurityScorecard
SecurityScorecard is the leading security ratings platform that enables you to instantly rate, understand, and continuously monitor the cybersecurity risk of any company, non intrusively. We automatically map ratings to cybersecurity questionnaire responses, providing a true 360 degree view of risk. SecurityScorecard Ratings uses non-intrusive and proprietary data collection methods, as well as trusted commercial and open-source threat feeds, to quantitatively evaluate the cybersecurity posture of any organization
SentinelOne
ServiceNow
SIOS Technology Corp.

For more than 20 years, SIOS has been helping companies protect their essential applications from downtime and disasters by providing reliable, easy-to-manage, clustering software and expert consulting services. Since then, we have stayed on the forefront of HA/DR and earned a reputation as the industry’s leading provider of high availability and disaster recovery protection.
SOC Prime
SonicWall
Spyderbat
STEALTHbits

Swimlane
Swimlane is the leader in AI-enabled, low-code security automation. Swimlane unifies security operations in-and-beyond the SOC into a single system of record to reduce process and data fatigue while quantifying business value and security effectiveness. The cloud-scale Turbine platform combines human and machine data into actionable intelligence for security leaders.
Tenable Inc.
ThreatConnect

ThreatQuotient

ThreatQuotient improves security operations by fusing together disparate data sources, tools and teams to accelerate threat detection and response. ThreatQuotient’s data-driven security operations platform helps teams prioritize, automate and collaborate on security incidents; enables more focused decision making; and maximizes limited resources by integrating existing processes and technologies into a unified workspace. The result is reduced noise, clear priority threats, and the ability to automate processes with high fidelity data. ThreatQuotient’s industry leading data management, orchestration and automation capabilities support multiple use cases including incident response, threat hunting, spear phishing, alert triage and vulnerability prioritization, and can also serve as a threat intelligence platform.
Trend Micro

Trend Vision One is a modern security operations platform for security and IT teams, unifying purpose-built XDR, attack surface risk management, and zero trust capabilities, in a single console. Trend Vision One correlates data across multiple security layers from native sensors and third-party data sources to rapidly discover, assess, prioritize, and mitigate risk across the attack surface.
Trend Micro Joint Solution Brief
Varonis

VMware
Webroot
Zscaler
Explore Partner Resources
Technology Alliance Partner (TAP) Program
TAP Program Inquiry Request
To request to become a technology partner and to view our Technology Alliance Partner (TAP) Program Guide, please fill out the following information.
Get Gartner’s complete analysis in the SIEM 2022 Magic Quadrant